Apple vs FBI: A Socratic dialogue on privacy and security
Updated on 05 April 2024
Diplo’s webinar on the Apple-FBI case, on 17 March (watch the recording):
evolved into a Socratic dialogue on the core concepts and underlying assumptions of the case. The lively debate inspired us to create a series of posts that argue the main dilemmas, played out by three fictitious characters, Privarius, Securium, and Commercias. The first starts with the main facts.
The Apple-FBI case triggered so many questions for which we do not have ‘correct’ or clear answers. Responses often trigger new questions. Join us in the debate with your comments and questions.
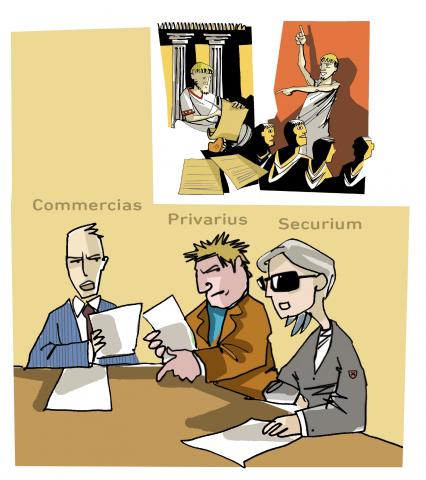
Commercias: A global debate indeed. Especially after Apple’s strong reaction. Declaring opposition to the order, Apple is arguing that by complying with the request, it would only create a dangerous precedent and would seriously undermine the privacy and security of its users. Other technology companies (such as Microsoft, Amazon, Google Facebook, and Twitter), as well as civil rights activists, have expressed support for Apple.
Privarius: Activists are also involved in this debate. The ruling, and the eventual outcome, can have very serious implications and repercussions. Encryption is a strong safeguard, and companies should not be made to weaken the security of their own products. Decryption should not be allowed.
Securium: Is it for companies to decide? US President Barack Obama has already objected to the creation of undecryptable black boxes, stating the need for a balance between security and privacy that would enable law enforcement authorities to continue doing their job. The outcome of this case is still unclear.
Commercias: Unclear indeed. Today’s court hearing was postponed, as the FBI said it may have found a way to unlock the phone without Apple’s assistance…
Privarius: This particular case may be nearing an end, but the main issues remain open. For example, how can there possibly be a balance between privacy and security if phones are rendered decryptable? After the Snowden revelations, it became clear that we can no longer completely rely on government agencies in ensuring our privacy, which is now in the hands of technology companies.
Commercias: Even the UN High Commissioner for Human Rights issued a statement, asking the US authorities to proceed with caution, as the case ‘could have extremely damaging implications for the human rights of many millions of people, including their physical and financial security’. The UN Special Rapporteur for freedom of expression also asked for caution, noting that the FBI request risks violating the International Covenant on Civil and Political Rights.
Securium: Whatever the outcomes will be, one thing is clear: even if a solution may have been found today, this does not solve the main dilemmas. So let’s see what the issues at stake are, starting with security…
The next post – published next Thursday, 24th March – tackles the security aspect. Stay tuned.


What we often disregard is
What we often disregard is that, besides security of the system/state, the essential component is the security of individuals. This goes from risks of terrorist attacks to risks of being hijacked or raped – and all those can be supported by digital means. There is nothing wrong with security service having the right to limit individual privacy (even though this too needs to be done through court order only) – like entering one’s apartment; but in such cases we should be sure that a) this doesn’t cause additional individual security of some persons b) this doesn’t have disproportionate effect on many other individuals. Technology is quite different from traditional space in that sense: unlike unlocking the apartment, inserting backdoor to technology endangers privacy of masses, not of a single user only. More importantly, this doesn’t only mean possibility of entering one’s photo book – this means enabling others, like criminals, to also be able to peek into one’s personal life more easily, which they use not for sake of amusement but for sake of criminal acts like extortion, profiling and robbery, or other assaults. The chain therefore looks like this: terrorist threat -> requesting to weaken security in technology -> inserting technology backdoor -> weakening security of equipment and services -> endangering privacy of masses -> endangering security of masses -> enabling additional criminal acts against individuals -> decreasing individual security of masses -> decreasing security. Such approach is counterproductive and doesn’t increase individual and overall security but, on contrary, may decrease it.
I don’t think it’s necessary
I don’t think it’s necessary to prioritise. Security, both State and personal is very important, as is privacy. If a State uses due process to collect evidence, as you say ‘to probe into the privacy of an individual who is a suspected criminal’ there is no violation of privacy. That’s not the issue here. However, requiring a manufacturer/developer to design and release technology to weaken privacy protections is different. While this debate has temporarily been suspended, this issue will have to be resolved. Is it really about just one phone? I don’t think so. See the next blog in this debate.
What ever direction the
What ever direction the argument goes, I strongly believe that the security of users especially at this moment when cyber crime and terrorism is on the rise is by far more important than their privacy. So for the sake of criminal investigations the state can use it’s intelligence service to probe into the privacy of an individual who is a suspected criminal.