
Apple vs FBI: It’s just one phone – or is it?
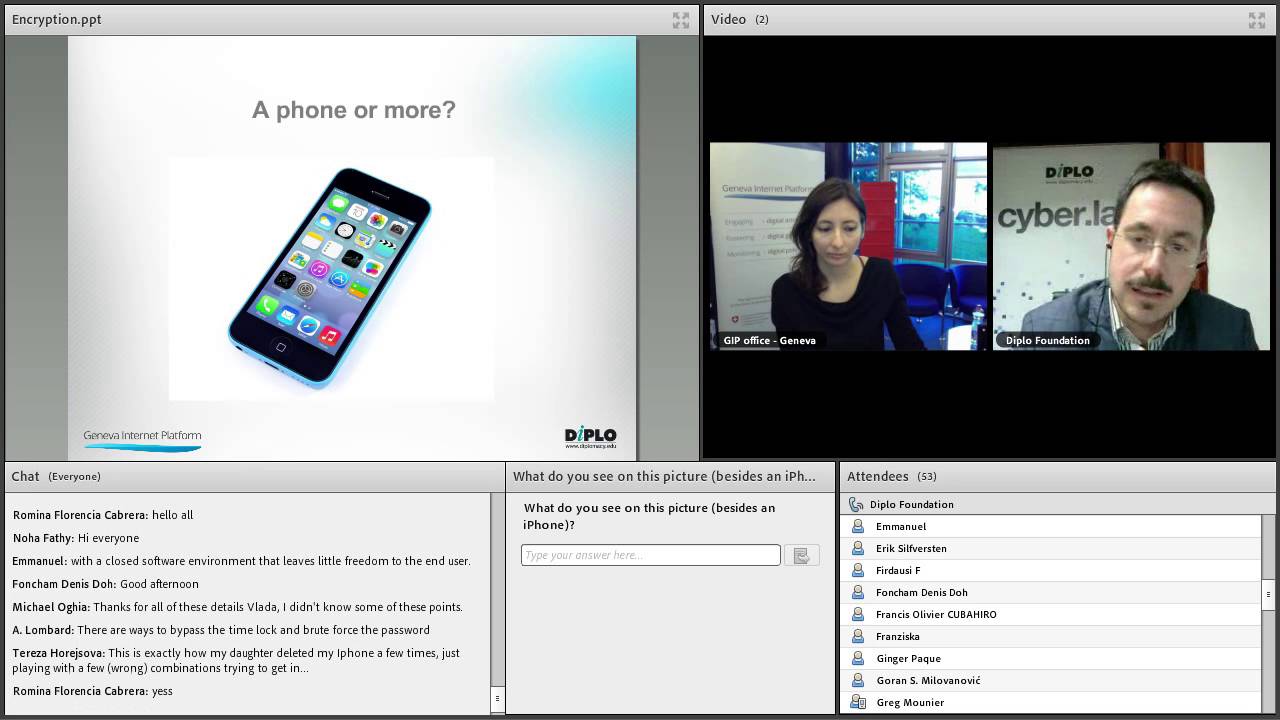
Diplo’s webinar on the Apple-FBI case, on 17 March (watch the recording):
evolved into a Socratic dialogue on the core concepts and underlying assumptions of the case. The lively debate inspired us to create a series of posts that argue the main dilemmas, played out by three fictitious characters, Privarius, Securium, and Commercias. While the first post tackled the main facts, the second builds on the narrative with security-related arguments. Join us in the debate with your comments and questions.

Securium: Isn’t this farfetched? The FBI’s requests are about one single iPhone: ‘… The Court’s order is modest. It applies to a single iPhone, and it allows Apple to decide the least burdensome means of complying. As Apple well knows, the Order does not compel it to unlock other iPhones or to give the government a universal “master key” or “back door”.’
Commercias: The order may not be referring to other phones, but if we take a look around us, we can see, for example, that the Manhattan district attorney has already indicated that there are currently 175 iPhones which investigators could not unlock, and he further confirmed that he would want access to all phones which are part of a criminal investigation, should the government prevail in the San Bernardino case. Apple is very likely to be compelled to use this technique to unlock iPhones in police custody all over America and beyond. Apple’s attorneys reported a list of nine other cases involving 12 different iPhones of different models that law-enforcement authorities had asked Apple to help crack, and none of them involved terrorism. We cannot run this risk.
Privarius: Apple needs to create new software to open this phone, and this software could potentially unlock any iPhone. There is no guarantee that the FBI will not use this software – or master key – again, and if it falls into the wrong hands, the software can be misused by third parties. One case will be followed by another and there won’t be an end.
Securium: We should focus on the case at hand. The order is a targeted one ‘that will produce a narrow, targeted piece of software capable of running on just one iPhone, in the security of Apple’s corporate headquarters. That iPhone belongs to the County of San Bernardino, which has consented to its being searched.’ We must also not forget that the phone was used by a terrorist who took innocent lives. Crucial information surrounding the case may be stored on this device. With this fact in mind, the court order is pretty reasonable!
Commercias: No, the fact that the court issued an order doesn’t necessarily mean it is reasonable. The fact is that Apple has been assisting the FBI in cases before this as well as in this one particularly – it has provided the backup of the phone stored within the iCloud (though, unfortunately, the last backup doesn’t contain the most recent files from the day of the shooting). The Internet industry has always been cooperative when court orders were issued (even without the court order, as we learned from Snowden). This time, what the court is requesting has crossed the line.
Securium: There are no red lines when it comes to protecting users and citizens worldwide.
Commercias: There are. The company has been asked to decrease its security level – which by the way is its corporate advantage – which helps keep users secure. If the court forces Apple to make a patch, this would reduce the security level of its system. And although the FBI has asked Apple to unlock only one iPhone, this might not be possible without affecting the privacy of all other iPhones, making them less secure in the process. Besides, do you really think that the FBI won’t use this ‘back door’? Once the privacy door is open, it will never be closed.
Securium: It is speculation. Let us not be abstract. Why would other phones be endangered?
Commercias: Technically speaking, Apple would need to create a software patch to its iOS, and install it in this particular phone. It is likely this could also be done within Apple’s headquarters, with the FBI accessing only this particular phone (even remotely) and without the chance to reach out to the particular software patch. However, since the phone needs to be handed over to investigators, there is a possibility of it being reverse-engineered. In addition, misuses and abuses cannot be fully controlled once the firmware is out.
Privarius: But let’s say, Apple creates a software patch to unlock the phone: authorities may still submit requests for hundreds of other phones to be unlocked, and requests could possibly come from other jurisdictions. In this case, Apple would need to have its teams constantly available. Moreover, future versions of the iOS would also need to have an updated patch. Ultimately, Apple might find it easier and cheaper to simply develop a real backdoor in its products, or to give up on the stronger security-by-design approach.
Securium: On the other hand, if Apple wins this court case – if the case is resumed – it can create a new precedent.
Privarius:… and a major win for privacy!
The next post, published on Saturday, 26th March, will tackle privacy and encryption. Stay tuned.

