
Most of us rely heavily on cloud services. The use of Gmail, Google docs, FlickR, Dropbox, iTunes are but a very few, common examples of cloud services which allow us to store our data online.
Yet most of us take these services completely for granted. Not the services themselves – we’re thankful that they exist. They allow us to access our data from wherever we are. Some are free to use. Some have larger storage capabilities.
What we often take for granted are legal issues, and issues related to security. For example, we rarely bother to find out in which country the servers are located. Servers located in other jurisdictions may have privacy laws, data protection laws, and a host of other laws which can be significantly different from the laws we’re used to. And we’re oh-so-quick to register for a service… without reading the terms of use.
The November IG webinar, hosted by Katitza Rodriguez, International Rights Director at the Electronic Frontier Foundation, tackled the issues and challenges related to cloud services, and the rules that can be put in place at national level to alleviate the heightened risk to privacy and other civil liberties.
Generally speaking, cloud computing issues relate to our online digital ‘footprint’. Our footprints include the data we upload, but also other details referred to as ‘metadata’, such as our IP address, our search history, our geo-location, and details related to our communications and interactions with others. This allows service providers to track our physical location almost all of the time, it allows them to make inferences or draw conclusions on private aspects of our lives, and it allows them to retain all this private data for decades.
Yet, governments also play a part. Another major issue relates to the right of law enforcement authorities, in some jurisdictions, to ask for data from service providers for surveillance purposes. This right is gradually expanding: legal provisions that broaden this right over a wider range of service providers are currently being debated in some countries. At the same time, surveillance ‘backdoors’ – which make it easier for authorities to have access to online communications – can create serious security vulnerabilities.
So what can be done to mitigate the risks? Online users can take various measures to protect data. These include encrypting data before uploading, and using encryption to protect emails. More information and tools on protecting content and communications are found on the Surveillance Self-Defence website, created by the Electronic Frontier Foundation.
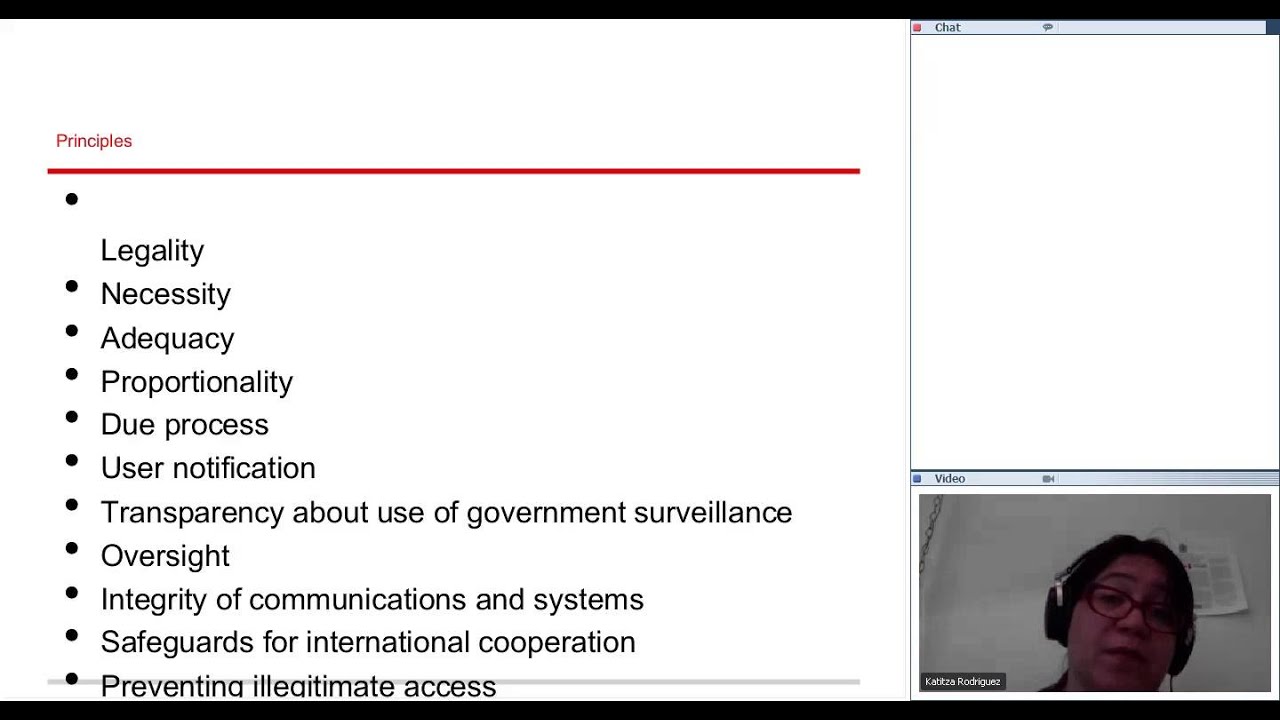
Rodriguez also said that a set of principles are needed to be established for governments and companies to adhere to. The principles – legality, necessity, adequacy, proportionality, due process, user notification, transparency about the use of government surveillance, oversight, integrity of communications, safeguards for international cooperation, prevention of illegitimate access, and cost of surveillance – were the outcome of a meeting of experts from civil society groups and industry which took place earlier this year. These principles represent a base level of protection, which matches the goals that human rights norms aim to safeguard.
Listen to or download the live recording of the webinar, in which our host Katitza Rodriguez discusses the issues mentioned above in more detail, as well as questions and comments raised by webinar participants:
To receive news and announcements about our IG webinars, subscribe to our IG webinars group.



