[Web discussion summary] Traceability and attribution of cyber-attacks: Who did it?

Author: Andrijana Gavrilović
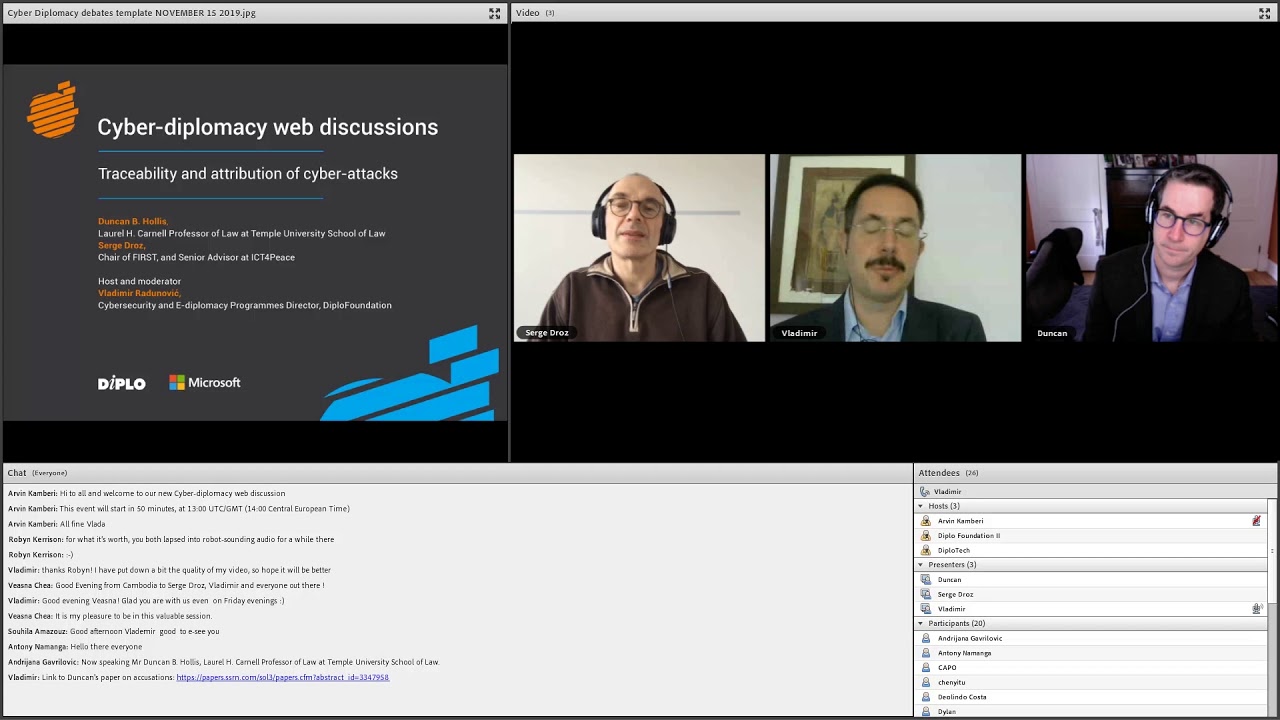
DiploFoundation, with the support of Microsoft, organised the Cyber-diplomacy web discussion: Traceability and attribution of cyber-attacks: Who did it? This webinar was the third in a series of cyber-diplomacy web discussions, following the web discussions: Cyber-armament: A heavy impact on peace, economic development, and human rights and Applicability of international law to cyberspace: Do we know the rules of the road? The series aims to map trends; introduce challenges; clarify open issues on the negotiation table; outline processes where discussions are happening; and explain how all of us can get involved.
What is the relation between an accusation and an attribution?
Duncan B. Hollis (Laura H. Carnell Professor of Law at Temple University School of Law), who recently published a paper on accusations and international law in cybersecurity, began by stating that there is a club of state and non-state actors that have the capacity to identify the author of a cyber-attack, either through technical means, or through technical means and secondary intelligence. Such accusations come from private sources, such as the Mandiant report which accuses advance threat actors connected to the Chinese government – referred to as Advanced Persistent Threat (APT) 1 – of a number of cyber operations, or other sources such as Kaspersky, CrowdStrike, and FireEye. In recent years, beginning roughly around the time President Obama alleged that North Korea was behind the Sony Pictures breach, states have started to get into the ‘accusations’ game. From an international relations and international law perspective, states accusing other states of bad behaviour in cyberspace is a new development. The Council on Foreign Relations tracker of cyber-attacks suggests that at least 25 nation-states have had the finger pointed at them. Dozens of accusations have been made against the USA, Russia, China, Iran, and the UK, but it is not clear whether these accusations have caused the accused to change their behaviour – we continue to see a rise in cyber operations.
Serge Droz (Chair of FIRST, and Senior Advisor at ICT4Peace) stated that there is an increasing number of attributions that are mostly finger pointing without a lot of substance. He agreed with Hollis that more solid reports come from the private industry (e.g. Mandiant) but also from academia (e.g. The Citizen Lab at the University of Toronto) and they confirm that proper attribution is possible. However, it is very hard to build a convincing case. States are very reluctant to show the evidence they have, not because it is hard to pinpoint which computer an attack came from, but because it is hard to pinpoint who is behind the attack. Technically, it may be able to trace the attack to the level of a keyboard, but jumping the 10 centimeters from the keyboard to the hand of a person to identify the attacker or an entity is a big challenge. To do this, signal intelligence and human intelligence are needed, and intelligence agencies that have access to them are reluctant to share. One of the challenges to solve is how to make attribution trustworthy, substantiating it to be defendable in court, in order to induce states to change their behaviour.
The process of attribution
Droz explained that the type of software used in a cyber-attack is determined first, closely followed by analysing the behaviour of the APT – Tactics, Techniques, and Procedures (TTP). Many actors replicate what they have done before, and use the same methods they previously used to break into foreign systems. Based on comparisons and patterns and a global overview (which private organisations have), cyber-attacks are grouped together and attributed to an actor. However, there is no guarantee that they were committed by the same actor.
Hollis affirmed that technical indicators of compromise tend to come from private sources. Private entities are trying to establish a reputation – like Mandiant did with the early attribution to APT1; increasingly, they may have the financial interest to share evidentiary support of their claim (e.g. CrowdStrike, a cyber-security intelligence company, had a billion dollar initial public offering).
States rarely disclose the means and methods used in an attribution; perhaps because their aim is not to convince anyone of it, but to warn the accused that the intrusion has been spotted.
Droz noted that states might also attribute cyber-attacks in order to not be seen as weak and doing nothing by their opponents. Another challenge is the possible reaction of states to being accused of a cyber-attack, as this might lead to strike back and escalation.
Reliability of attribution
The reliability of attribution depends on how the state wants to follow up, Droz commented. If it intends to name and shame another state, it needs solid evidence. However, if the state intends to strike back, it may be expected that it has concrete proof.
Hollis noted that there is an absence of laws in attributions and accusations made outside of the domestic indictment context. For example, when President Obama accused North Korea of hacking Sony Pictures, it was characterised as ‘cyber vandalism’; the accusation that Russia interfered in the US presidential election was characterised as a ‘violation of international norms’. The absence of laws in accusations could be explained by states wanting to preserve their own ability to conduct such activities: the ambiguity of laws, lack of evidence that is firm enough to sustain a legal claim or a decision to not distract from the political conversation with the legal context. It is important to determine what is the appropriate level of proof that a state or a non-state actor would be expected to provide.
Droz highlighted that there is an informal unwritten agreement between members of the technical community on what constitutes convincing arguments, but it has never been put on paper. Quality checks or peer reviewing of analyses should exist, but currently do not because there are no standards in place. Standards for network-based attacks and global attacks are slowly being developed. CyberPeace Institute, established in Geneva by Microsoft and its partners, may take a role of developing a common methodology in this regards.
Hollis noted that collective attribution is emerging and that information sharing between them is occurring behind the scenes. For instance, more than one government accused North Korea of WannaCry. Multiple states have also accused the Russian military agency’s GRU for their alleged activity.
Who should do attribution?
Droz stated that fact-finding and final attribution could be separated. Fact-finding can be done by a lot of players, but attribution to a state might have to be kept as the exclusive right of states. Who does which part of the attribution needs to be negotiated.
Hollis agreed that disaggregated attributions should be welcomed. As there are no standards in place yet, it could be useful for many actors to participate in the process of attribution in order to determine which is the most effective. In Hollis’ opinion, attribution may be an insufficient term, as attribution is just fact-finding. A cyber-attack can be attributed to a person, territory, or a machine. Another factor to be taken into account is exposure – it is possible and probable that there are attributions that are being communicated between the accuser and the accused in private or closed settings. The third factor to be taken into account is the condemnation that the accuser is making – condemning the actors as a matter of domestic law, international law, or norms.
What are the consequences?
One possible scenario is that the accused state changes its behaviour after a naming and shaming campaign. However, this result is not likely among major military powers, for instance in the case of Western-led accusations against their adversaries such as Iran, Russia, North Korea. An accusation could have a defensive purpose – technical details of an accusation could be shared to help others to defend against similar malware. It could also be constitutive – the accuser could be trying to establish whether a cyber-attack goes against a norm or a law. Another purpose could be deterrence, as potential malicious actors would be aware that they will be named should they engage in a cyber operation – moreover that a response of some sort may follow. While we usually look at how big players would act and react, it is important to remember that ongoing conflicts exist around the world, and cyber may become part of tensions or conflicts across Africa, the Middle East or elsewhere – careless mutual accusations there may lead to further escalation of conflicts.
What should we do next?
Droz advised that we should accept the fact that cyber operations are going to take place. Hollis stressed that capacity-building for actors outside the traditionally European-focused dialogue is necessary; they should have the capacity and the resources to be able to know when they, their industry, or civil society are being targeted. Work on establishing common methodologies for technical and legal attribution should be expanded.